In 2025, Argentina shows what happens when the state’s promise collapses faster than its currency. When annual inflation breached the 200% mark, the peso did more than lose value. It lost its status as a shared reality.
President Javier Milei has responded with an aggressive ritual of “Sovereign Choreography.” He has secured a $20 billion International Monetary Fund (IMF) facility. He is also prioritizing payments to bondholders to restore external credit. But beneath this performance of formal solvency, the citizens have already exited the system. Argentina has become the world’s first dual-ledger republic.
The Rise of Crypto Sovereignty
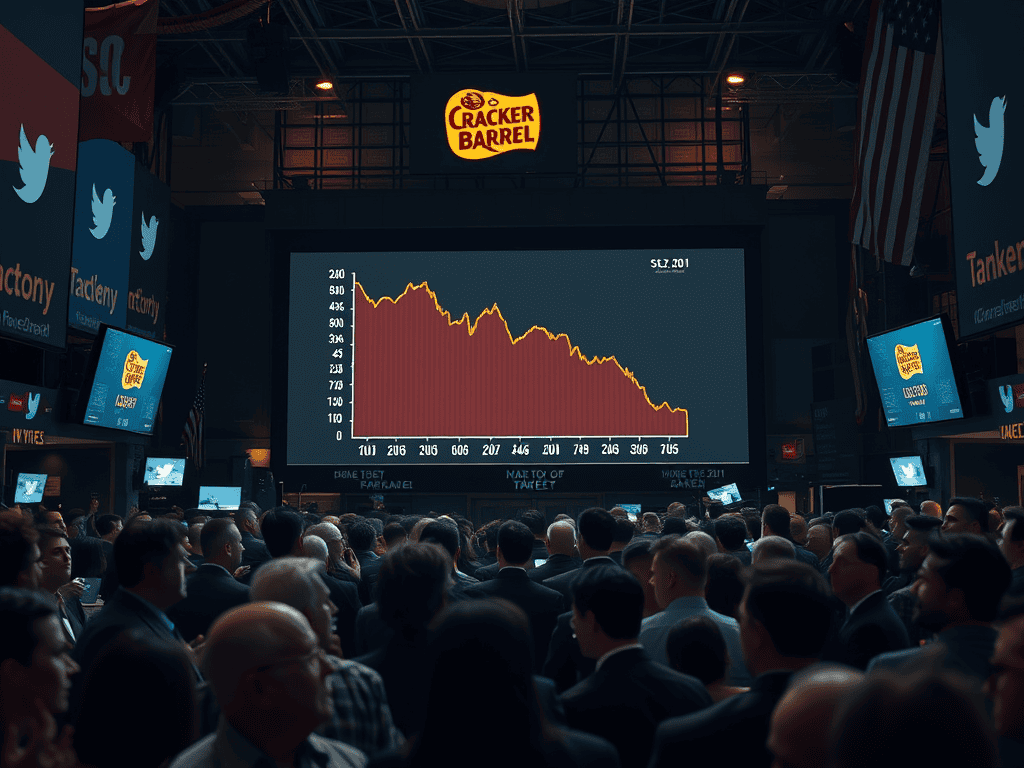
Between 2022 and 2025, Argentina processed nearly $94 billion in crypto transactions. This achievement resulted in one of the highest crypto-to-GDP ratios on the planet. This is not a speculative boom; it is the emergence of Crypto Sovereignty.
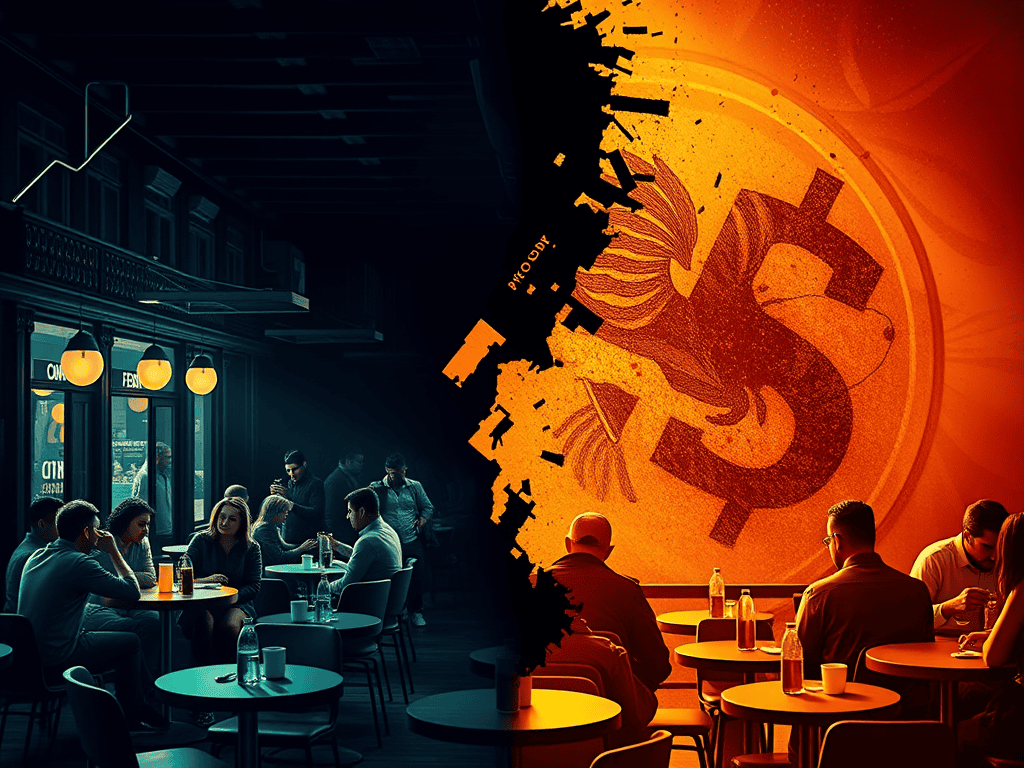
In Buenos Aires, the transaction is no longer an act of rebellion—it is an act of survival. Every café, contractor, and freelancer now operates with two prices: pesos for formality and stablecoins for certainty. The Argentine citizen uses stablecoins like USDT and USDC on Ethereum rails. This choice effectively bypasses the central bank. It helps find a more reliable ledger of belief.
Argentina’s sovereignty has split. One version is performed for the IMF. It is managed via austerity and debt repayment. The other is staged by the citizens. This happens via decentralized protocols. The state handles the optics, while the blockchain handles the liquidity.
Ethereum as the National Mirror
The hosting of the Ethereum World’s Fair in Buenos Aires (November 2025) served as a live demonstration of this shift. It was more than a tech conference; it was a rehearsal for a new form of governance.
Citizens transact, verify, and coordinate entirely on-chain. They are not just using a tool. They are auditing the failure of the state. The blockchain provides the transparency and finality that the central bank cannot. In this environment, the “Regulatory Vacuum” becomes an opportunity for crypto growth.
The Regulatory Vacuum—Who Audits the Bypass?
A profound oversight gap has emerged as the state’s gatekeepers fail to track the citizen migration.
- The IMF’s Blind Spot: International monitors focus on national balance sheets. They also pay attention to M2 aggregates. However, they are structurally unable to see the shadow liquidity of the blockchain.
- Central Bank Irrelevance: The central bank enforces credit optics, but it no longer controls the liquidity of the street.
- Diffusion of Power: State sovereignty has not disappeared; it has diffused into the code. Regulation lags because it is still trying to govern the “territory” while the “capital” has moved to the rail.
Conclusion
Argentina is not collapsing; it is rehearsing a new form of belief. The country has proven that when a currency breaches its social contract, the market will spontaneously manufacture its own legitimacy. The question for every republic is no longer “Will crypto replace the state?” but rather “Which ledger will the citizen choose to believe?” In the dual-ledger prototype, the state keeps the debt, but the citizens keep the liquidity. The stage is live, the choreography is split, and the future of sovereignty is being settled on-chain.
Further reading: