Summary
- Heist as Signal: The October 2025 Louvre jewel theft exposed not just cultural vulnerability but the question of how stolen value can be converted into instant liquidity through digital rails.
- Tokenized Fencing: NFTs can be minted as “digital twins” of stolen artifacts, allowing illicit actors to sell the story rather than the object. Provenance becomes marketing, not protection.
- Stablecoin Exit Rails: Proceeds can be rapidly converted into USDC, USDT, or PYUSD, providing borderless liquidity. This isn’t a flaw in stablecoins themselves, but a misuse of their speed and accessibility.
- Red‑Flag Architecture: Mixers, cross‑chain bridges, and anonymous marketplaces fragment visibility. Buyers and platforms must treat provenance as a security control, escalating suspicious listings early.
The Heist Isn’t the Lesson. The Liquidity Path Is.
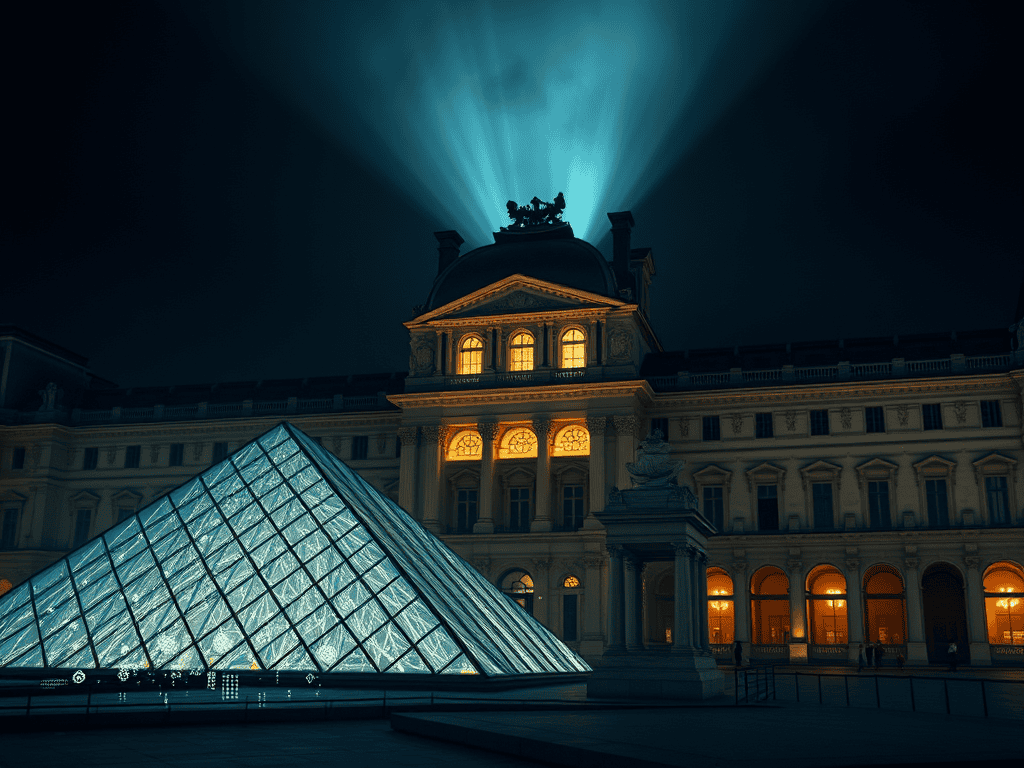
On 19 October 2025, a daylight smash‑and‑grab at the Louvre’s Galerie d’Apollon shocked global audiences. Eight historic jewels vanished in minutes. No evidence links this crime to crypto. But the heist raises a deeper structural question: when cultural property disappears, how easily can illicit value be converted into instant liquidity? This question connects directly to the broader debate on stablecoin sovereignty explored in The Algorithmic Border: Why Stablecoin Sovereignty Is the New Quant Frontier.
Where that article maps sovereign control of stablecoin corridors, this article examines how those same rails can be misused in cultural theft.
How Stolen Value Travels Without Moving the Object
Tokenized fencing doesn’t rely on selling the artifact itself — it relies on selling the story. A fence can mint an NFT claiming to represent a “digital twin” of the stolen item. Buyers speculating on rarity or myth may transact without confirming physical custody. In this model, the token becomes the tradable object; the jewel is just the pretext.
This mirrors the cornerstone’s argument: narrative liquidity is as powerful as sovereign liquidity. Provenance becomes marketing, not protection.
The Instant Liquidity Layer: Stablecoins as Exit Rails
Once a token sells, proceeds can be converted into USDC, USDT, or PYUSD. These stablecoins provide fast, borderless liquidity, unconstrained by banking hours or geography. They are widely accepted across exchanges, OTC desks, and DeFi platforms.
This isn’t a flaw in stablecoins themselves — it’s a misuse of their liquidity properties. The same stablecoin properties that enable sovereign visibility in The Algorithmic Border — speed, borderless reach, and interoperability — can also be exploited for opacity when misused. The rails are neutral; the use case defines the risk.
The Corridors of Obfuscation: Mixers, Bridges, Layering
To obscure the trail, illicit actors may route funds through privacy mixers, cross‑chain bridges, or rapid‑hopping wallets. The U.S. Treasury’s 2022 sanctions against Tornado Cash showed how mixers can sever provenance links. Each blockchain hop fractures visibility, making compliance harder.
This is the shadow frontier of the quant border: fragmentation as camouflage.
Selling the Story Instead of the Stone
Tokenizing stolen items is often not about transferring the object at all. Fractionalization allows multiple buyers to take positions in the “idea” of an asset. The speculative layer becomes its own market. The object remains hidden; the story circulates freely.
This parallels the cornerstone’s thesis: in digital markets, narrative itself becomes the warehouse of value.
Red‑Flag Architecture for Buyers and Platforms
- Provenance Gaps: Missing custody records, unverifiable ownership, sudden timeline jumps.
- Funds Pathology: Stablecoin payments routed to fresh wallets, offshore OTC desks, or peer‑to‑peer corridors.
- Marketplace Suspicion: Anonymous storefronts, no KYC, listings heavy on myth but light on documentation.
- Technical Traces: Wallets linked to mixers, sanctioned addresses, or high‑risk jurisdictions; immediate fragmentation after sale.
Conclusion
The Louvre theft is a reminder that cultural theft is ancient, but laundering rails are new. Tokenized fencing doesn’t require a shadow auction; it requires a buyer who values narrative, speed, and anonymity. Stablecoins don’t cause crime, but without robust platform controls, they accelerate value mobility.
This article complements The Algorithmic Border by showing the illicit mirror image of stablecoin sovereignty. Where The Algorithmic Border article maps sovereign control, this article maps how the same rails can be misused. Together, they frame the dual frontier: stablecoins as instruments of both quant sovereignty and narrative laundering.
Truth Cartographer maps detection signals as educational due‑diligence frames — not legal advice.